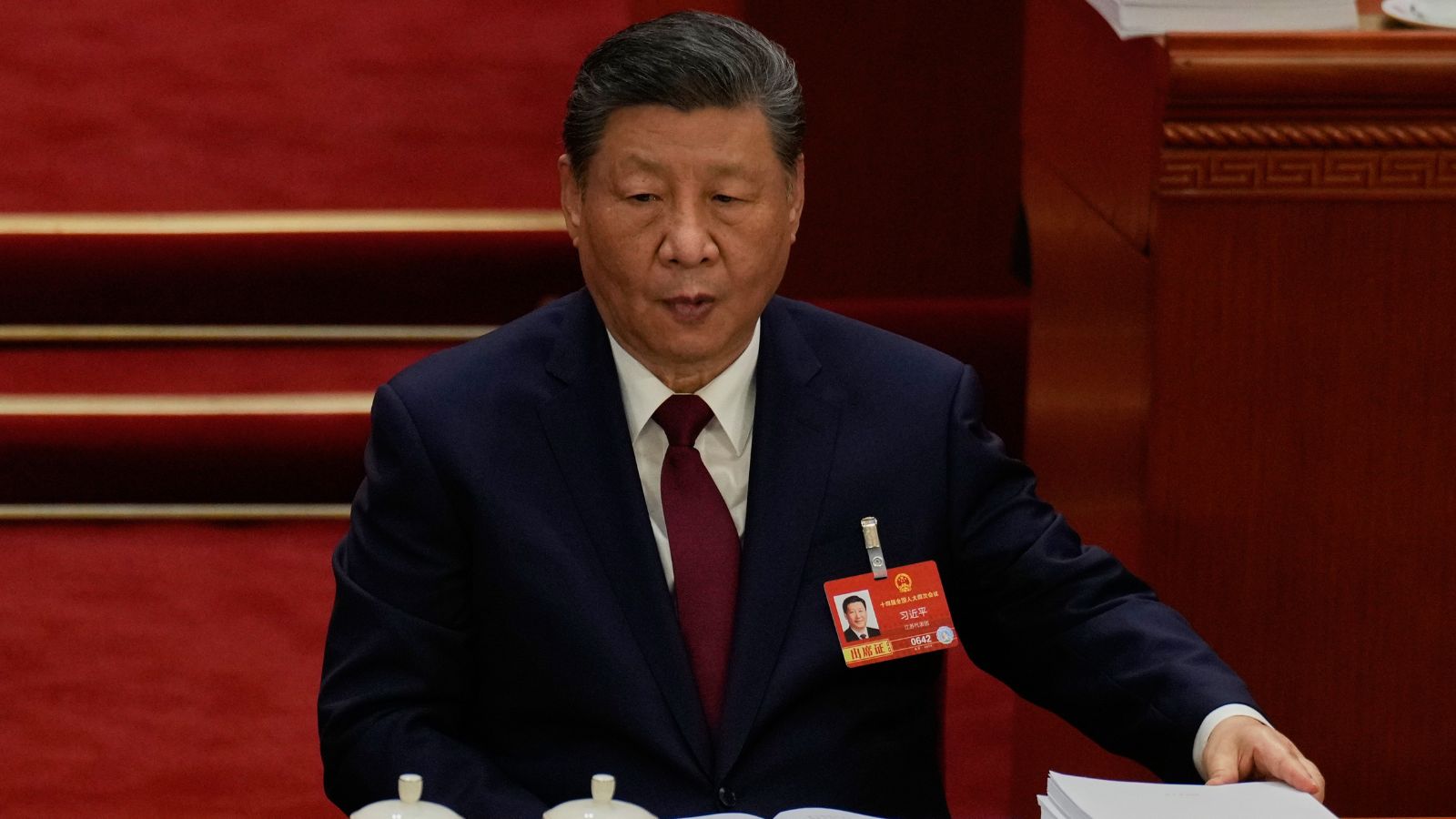
The Chinese Communist Party has shifted its primary economic objective from unconstrained growth to "security-centered development," a transition that redefines technology not as a commercial asset but as the foundational layer of national sovereignty. This strategy acknowledges a terminal breakdown in the post-1990s era of globalized supply chains and replaces it with a closed-loop industrial system designed to withstand prolonged external decoupling. The current trajectory is an attempt to solve the "Malacca Dilemma" of the digital age: the reality that China’s industrial apparatus remains dependent on Western-controlled intellectual property and silicon bottlenecks.
The Triple-Axis Framework of Chinese Tech Insulation
China’s response to U.S. export controls and the "Small Yard, High Fence" policy is categorized into three distinct operational axes. This framework moves beyond the vague concept of "innovation" into specific tactical domains of industrial survival.
1. The Chokepoint Elimination Vector (Kakaweizi)
The immediate priority is the systematic identification and replacement of 35 critical technologies where China lacks domestic alternatives. This list, popularized by the state-owned Science and Technology Daily, includes photolithography machines, high-end chip design software (EDA), and ultra-pure chemicals for semiconductor fabrication.
The logic here is purely defensive. By subsidizing "Little Giants"—specialized Small and Medium Enterprises (SMEs) that dominate narrow, high-barrier niches—Beijing is attempting to build a domestic "Mittelstand" similar to Germany’s. The goal is to ensure that no single component in the value chain can be used as a geopolitical lever by Washington.
2. Infrastructure as a Forcing Function
Unlike the U.S. model, which relies on private sector demand to pull technology forward, the Chinese model uses state-led infrastructure deployment to push technology into the market. This is evident in the "New Infrastructure" plan (Xinjian).
- 5G/6G Saturation: Deploying the world’s largest 5G network creates a laboratory for industrial IoT (IIoT) that doesn't exist elsewhere.
- The East-to-West Computing Resource Initiative: By building massive data center clusters in the energy-rich western provinces to process data from the coastal east, China is attempting to commoditize high-performance computing power for its domestic AI industry, bypassing the need for certain high-end distributed server architectures.
3. Standards Hegemony and the "China Standards 2035"
The long-term play involves moving from a "technology consumer" to a "rule-maker." By embedding Chinese specifications into international bodies (ISO, IEC, ITU), particularly in emerging fields like quantum communication, smart cities, and satellite internet (the G60 Starlink competitor), China aims to create a path dependency for the Global South. If the foundational protocols of the next internet are Chinese, the efficacy of U.S. sanctions diminishes significantly.
The Cost Function of Forced Substitution
The transition to a self-reliant technology stack is not a Pareto improvement; it carries significant, quantifiable costs that the Chinese leadership has deemed acceptable in exchange for security.
The Efficiency-Resilience Trade-off
In a globalized market, firms select the most efficient components based on price and performance. Forced localization compels Chinese firms to use domestic "substitutes" that are often more expensive and less capable. This creates a "hidden tax" on Chinese manufacturing. For example, a Chinese EV maker using domestic automotive-grade chips instead of Nvidia or TI silicon may face higher failure rates or lower energy efficiency, reducing their global competitiveness in the short term.
Capital Misallocation and the "Big Fund" Leakage
The National Integrated Circuit Industry Investment Fund (the Big Fund) has poured over $100 billion into the semiconductor sector. However, the lack of market-driven discipline has led to "zombie" projects and massive corruption. The mechanism of state-led investment often prioritizes "hard tech" (hardware) over "soft tech" (software ecosystems), resulting in a surplus of low-end fabrication capacity while the most sophisticated logic chips remain elusive.
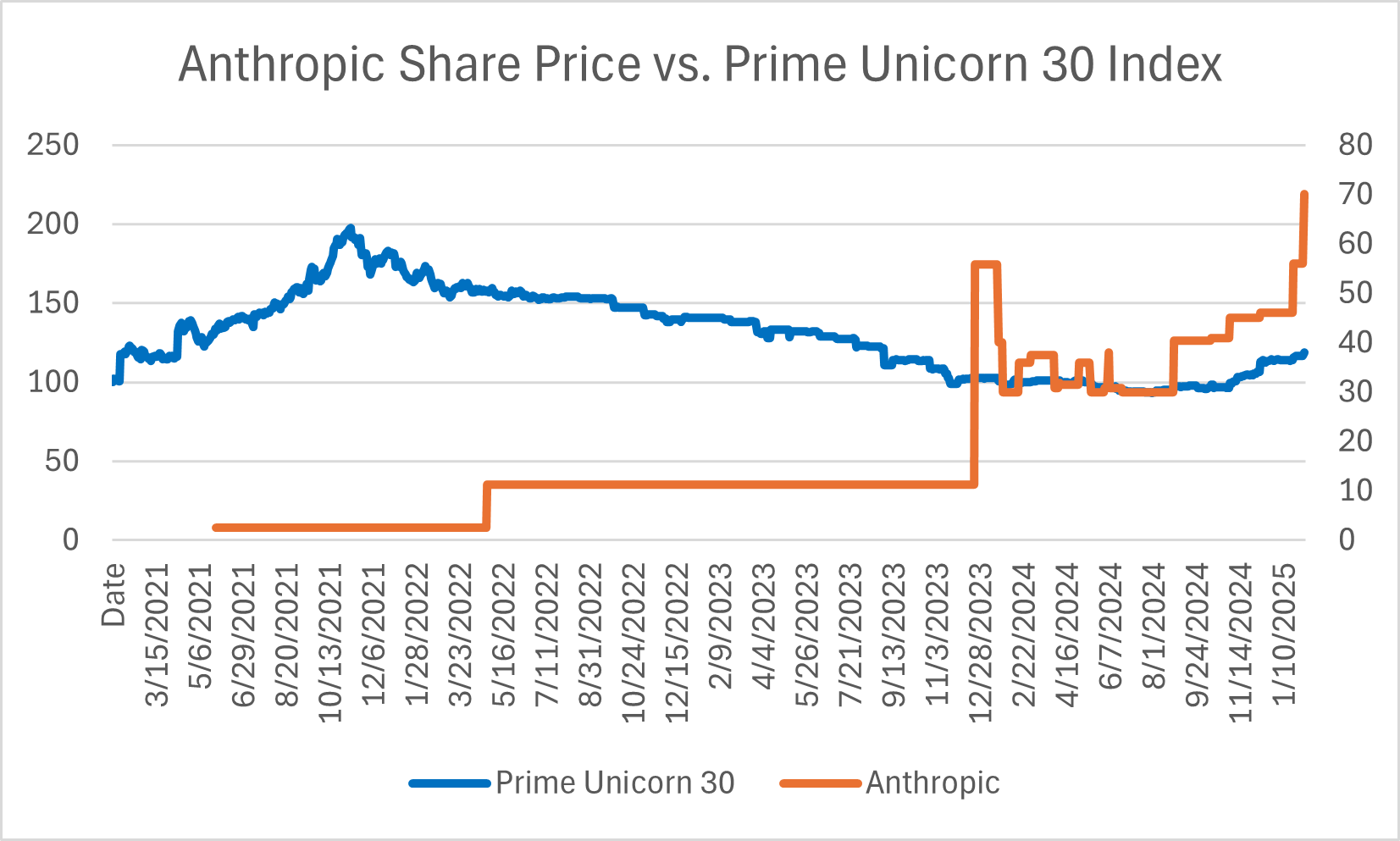
Quantifying the Silicon Bottleneck
The effectiveness of China’s strategy is ultimately measured against the "node gap" in semiconductor manufacturing.
$$G = N_{global} - N_{domestic}$$
Where $G$ represents the generational gap in nanometers. Currently, while the world moves toward 2nm and 3nm mass production, China’s SMIC is stabilized at 7nm (via DUV multi-patterning) but faces a steep physics and cost barrier to reach sub-5nm without EUV (Extreme Ultraviolet) lithography.
The strategic response is not to chase the leading edge in every category, but to dominate "Legacy Chips" (28nm and above). These are the chips that power cars, washing machines, and military hardware. By flooding the global market with cheap, reliable legacy silicon, China creates a reverse-dependency: the West becomes reliant on China for the foundational components of its industrial base.
The Structural Realignment of Private Capital
The "Common Prosperity" era has fundamentally altered the incentives for China’s tech titans. The era of consumer internet dominance (Alibaba, Tencent) is being forcibly wound down in favor of "Hard Tech" (Huawei, BYD, DJI).
This is a shift from Capital Gains to Strategic Utility. Venture capital in China is being redirected by government-guided funds (GGFs) toward:
- Material Science: High-strength carbon fibers and rare earth processing.
- Biotech: Genomics and synthetic biology for food security.
- Energy Storage: Solid-state batteries and green hydrogen.
The "Red Queen" effect is in full play: Chinese firms must run twice as fast just to maintain their current position relative to Western sanctions. To mitigate this, China is leveraging its massive domestic market—the "Dual Circulation" strategy—to provide the necessary scale for these nascent technologies to mature before they are exported.
The Asymmetric Vulnerability of Information Ecosystems
A critical oversight in most analyses is the divergence between hardware independence and software ecosystem dominance. While China can manufacture a smartphone entirely with domestic parts, it cannot easily replace the Android/iOS duopoly or the global dominance of Windows/Linux in the enterprise space.
The development of HarmonyOS (Huawei) and EulerOS represents an attempt to build a sovereign software stack. The difficulty is not the code, but the network effects. A technology ecosystem is a two-sided market; without developers, the hardware is inert. China’s strategy here is coercive: mandating that all government and state-owned enterprise (SOE) offices replace foreign hardware and software (the "3-5-2" policy) within specific timeframes. This provides a guaranteed user base of approximately 30 million people, a sufficient "beachhead" to sustain a domestic software industry.
[Image comparing the U.S. and Chinese technology stacks across 7 layers]
Risks to the Autarky Thesis
The primary threat to this strategy is not external pressure, but internal demographic and fiscal constraints.
- Human Capital Depletion: The "Thousand Talents" program and its successors face increasing headwinds as Western universities tighten vetting. The localized "brain drain" of talent moving from the private sector to the slower-moving SOE sector reduces the overall velocity of innovation.
- The Debt-Innovation Trap: R&D is capital-intensive and high-risk. As local governments face a debt crisis stemming from the property sector collapse, their ability to provide the "patient capital" required for deep-tech breakthroughs is diminishing.
- The Isolation Paradox: By cutting itself off from global standards to ensure security, China risks developing "Galapagos technologies"—systems that work perfectly within the mainland but are incompatible with the rest of the world, making the Belt and Road Initiative increasingly difficult to implement.
Strategic Direction for the 2026-2030 Cycle
The next phase of China’s tech resistance will focus on Integrated Photonic Circuits and Quantum-Resistant Cryptography. These are fields where the "first-mover advantage" of the U.S. in traditional CMOS (Complementary Metal-Oxide-Semiconductor) technology is less pronounced.
Organizations operating within this ecosystem must prioritize "Sanction-Resilient" architectures. This means:
- Developing AI models that are "compute-efficient" to reduce reliance on H100/B200 level GPUs.
- Aggressively pursuing "RISC-V" architecture as the universal, open-source ISA (Instruction Set Architecture) to replace ARM and x86.
- Integrating "Dual-Track" supply chains, where a Chinese domestic-only production line mirrors an international one.
The final strategic move for Beijing is to convert its dominant position in "Green Tech" (EVs, Solar, Batteries) into a geopolitical counter-leverage. By controlling the components for the world’s energy transition, China aims to make the "Small Yard, High Fence" strategy too expensive for the West to maintain. The endgame is not parity, but an asymmetric interdependence that makes decoupling a mutual suicide pact.
The blueprint for Western firms is to identify and protect "High-Value Asymmetries" while acknowledging that the era of a single, unified global technology market has ended. Firms must now operate within a bifurcated reality where "security" is the primary input in every technical specification.