In a small, windowless office in downtown Jakarta, a sysadmin named Adi watches a progress bar that hasn't moved in forty minutes. Outside, the humid air is thick with the scent of clove cigarettes and exhaust. Inside, the air is sterile, chilled by an overworked AC unit that rattles in its housing. Adi isn't a soldier. He isn't a politician. He’s a guy who worries about his daughter’s tuition and whether the office coffee machine will finally die.
But as a screen flicker signals the collapse of his company’s regional database, Adi has just become a casualty in a war being fought four thousand miles away.
When we talk about conflict in the Middle East, we tend to think in terms of geography. We look at maps of the Levant or the Persian Gulf. We track the flight paths of drones and the trajectory of missiles. We treat the "blast radius" as something measured in meters of concrete and scorched earth.
We are wrong.
In the modern age, the blast radius of a kinetic war is elastic. It stretches through submarine fiber-optic cables, bounces off satellites, and settles into the servers of a logistics firm in Vietnam or a bank in Manila. Southeast Asia, a region once considered a distant bystander to the volatile friction between Iran and its adversaries, is discovering that in a connected world, there is no such thing as a "safe distance."
The Invisible Shrapnel
Imagine a digital reservoir. For years, state-sponsored hacking groups—let’s call them the "A-teams" from Tehran, Tel Aviv, and beyond—have been filling this reservoir with sophisticated tools. These are not your neighborhood teenager’s viruses. These are surgical instruments designed to dismantle power grids, intercept diplomatic cables, and freeze financial systems.
When a hot war breaks out, the reservoir overflows.
This isn't always intentional. Often, it is the result of what security analysts call "automated spillover." A piece of malware designed to target a specific piece of industrial software in a Mediterranean port doesn't stop at the border. It looks for its prey everywhere. If a shipping company in Singapore uses that same software, the malware strikes. It doesn't ask for a passport. It doesn't care about ASEAN’s policy of neutrality.
But there is a darker, more deliberate side to this. Iran has long viewed Southeast Asia as a secondary theater for influence and asymmetric pressure. As the pressure mounts at home, the need to strike at "soft" targets abroad increases.
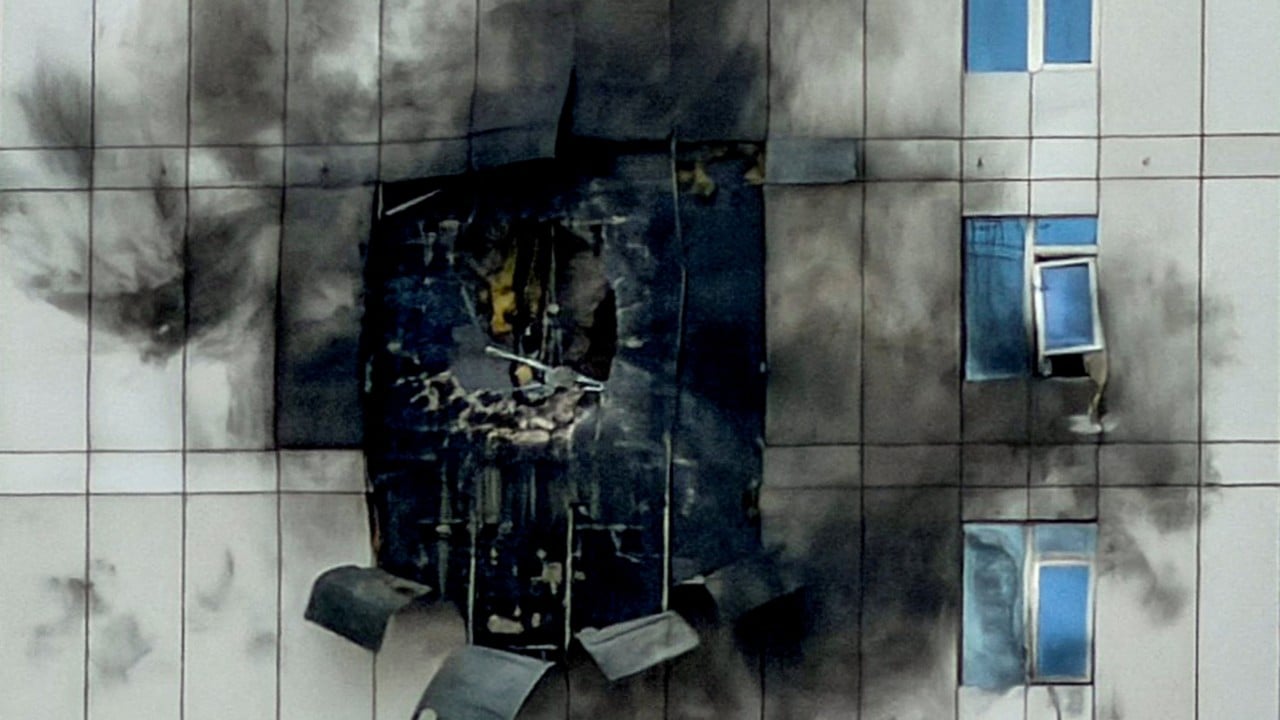
Consider a hypothetical scenario involving a regional hub like Kuala Lumpur. A state actor doesn't need to bomb a building to cause chaos. They just need to delete the digital identities of ten thousand travelers, or lock the cooling systems of a data center holding the records of a regional venture capital firm. The goal isn't necessarily destruction; it’s distraction. It’s about forcing the world to look away from the front lines and deal with the fire in their own backyard.
The Cost of the Middleman
The complexity of Southeast Asia’s supply chains makes it the perfect conductor for digital shockwaves. Most of the world’s semiconductors, garments, and electronics pass through these ports. If a cyberattack slows down a single terminal in the Port of Tanjung Pelepas for even twelve hours, the ripple effect reaches the shelves of a grocery store in London and a car factory in Detroit.
We often assume that because a conflict is religious or territorial in nature, its weapons will be too. But cyber warfare is the ultimate equalizer. It’s cheap, it’s deniable, and it’s infectious.
For the medium-sized businesses that form the backbone of the Indonesian or Thai economies, the defense budget for a state-level cyber attack is exactly zero dollars. They are playing a game of high-stakes poker with a hand of cards they didn't even know they were holding.
Adi, our sysadmin in Jakarta, isn't fighting a hacker. He is fighting an algorithm that was written by a genius in a bunker, funded by a national treasury, and unleashed for reasons that have nothing to do with him. He is the collateral damage of a twenty-first-century siege.
The Vulnerability of the Tiger
Why Southeast Asia? Why now?
The region is currently undergoing a "digital sprint." From the rural villages of Cambodia to the high-rises of Bangkok, millions of people are coming online for the first time via mobile devices. This rapid expansion is a miracle for poverty reduction, but it’s a nightmare for security. It’s like building a city of glass skyscrapers without ever inventing the concept of a lock.
The infrastructure is often a patchwork of legacy systems and brand-new tech, held together by hope and duct tape. In this environment, a "wiper" virus—a type of malware that simply deletes everything it touches—doesn't just cause a hiccup. It causes a total system failure.
During the height of the Stuxnet era, the world realized that code could break machines. Today, the world is realizing that code can break countries.
If the conflict in Iran escalates, we shouldn't just be looking for the next missile launch. We should be looking at the sudden, unexplained outages at regional banks. We should be looking at the "glitches" in the air traffic control systems of burgeoning mega-cities. These aren't accidents. They are the shrapnel of a distant explosion hitting the target.
Beyond the Firewall
There is a temptation to think that better software is the answer. If we just buy the right "robust" security suite or "leverage" the right "cutting-edge" AI, we’ll be safe.
That is a comforting lie.
The real vulnerability isn't in the code; it’s in the connection. We have built a world where everything is linked, but no one is responsible. We have prioritized speed over stability, and now the bill is coming due.
For the people on the ground in Ho Chi Minh City or Jakarta, the threat isn't a shadowy figure in a hoodie. The threat is the sudden silence of a phone that won't connect, the blank screen of an ATM, and the realization that the "blast radius" of global politics has finally reached their front door.
The sysadmin in Jakarta finally gives up on the progress bar. He sighs, picks up his phone, and tries to call his wife. The call doesn't go through. The network is congested, or perhaps something more sinister is happening at the exchange.
He looks out the window at the skyline, a shimmering grid of lights that depends entirely on things he can no longer control. He wonders if someone in a room halfway across the world just flipped a switch because they were angry at someone else he’s never met.
The air conditioner rattles one last time and goes quiet. The office begins to warm. Outside, the city carries on, unaware that the invisible shrapnel is already in the air, moving at the speed of light, looking for a place to land.
The screen on Adi’s desk suddenly turns a deep, bruised purple, and then, it simply goes black.